As WordPress brute force attacks are on the rise and without any signs of slowing down, preventing brute force attacks on your WordPress site is critical to your site’s security and stability. In this article, we will show you how to use iThemes Security to easily block brute force attacks using their cloud-based database.
- First, log into your WordPress admin dashboard.
- This article assumes that you already have iThemes Security installed. If you do not already have it installed, you may follow our guide on installing iThemes Security.
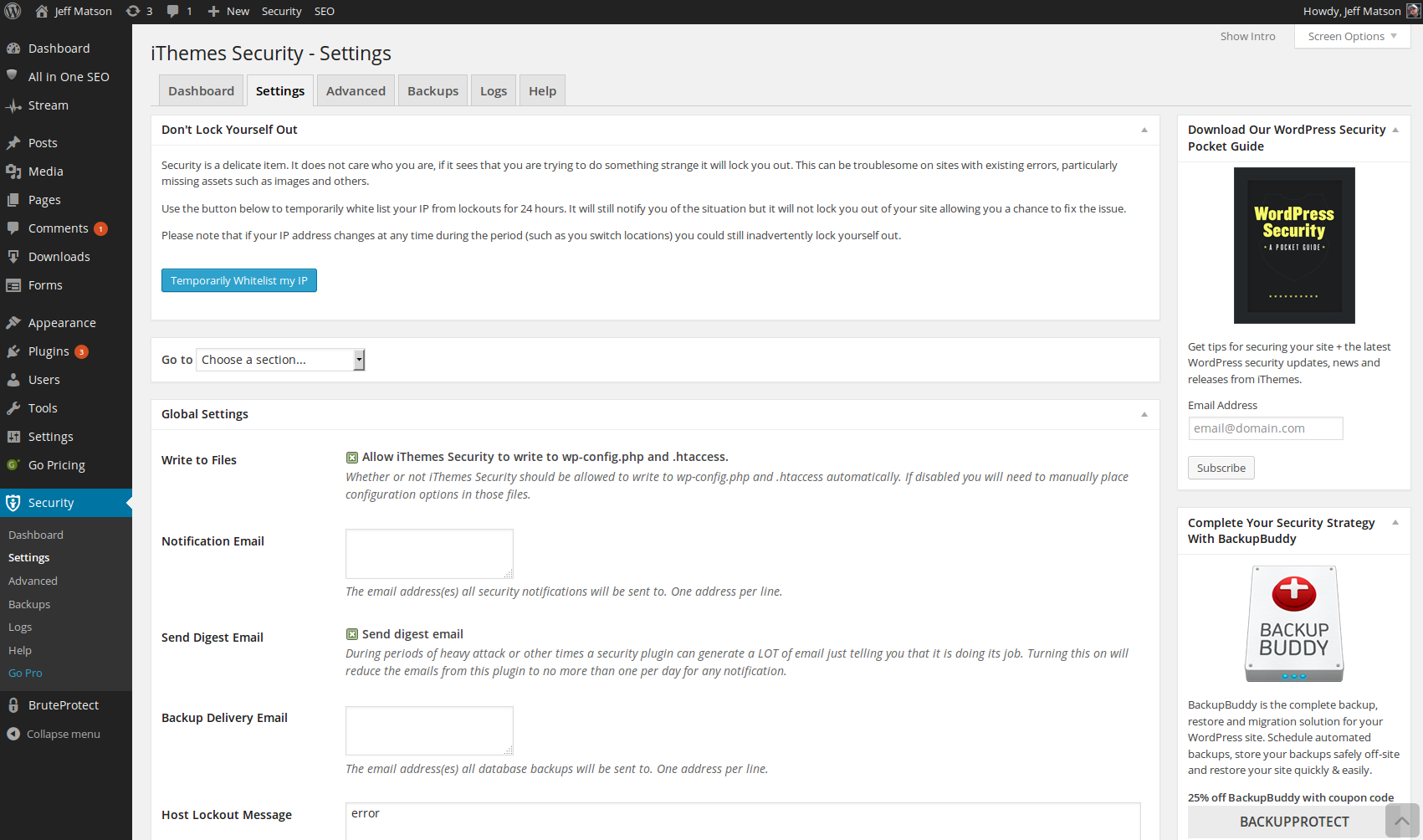
Within your WordPress admin dashboard, hover over Security on the left side menu and click on Settings.
Next, scroll down to the Brute Force Protection section.
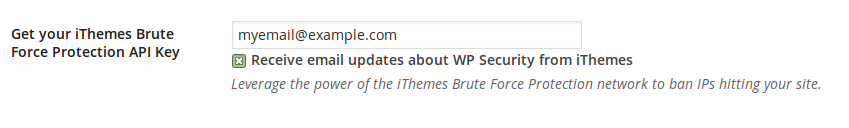
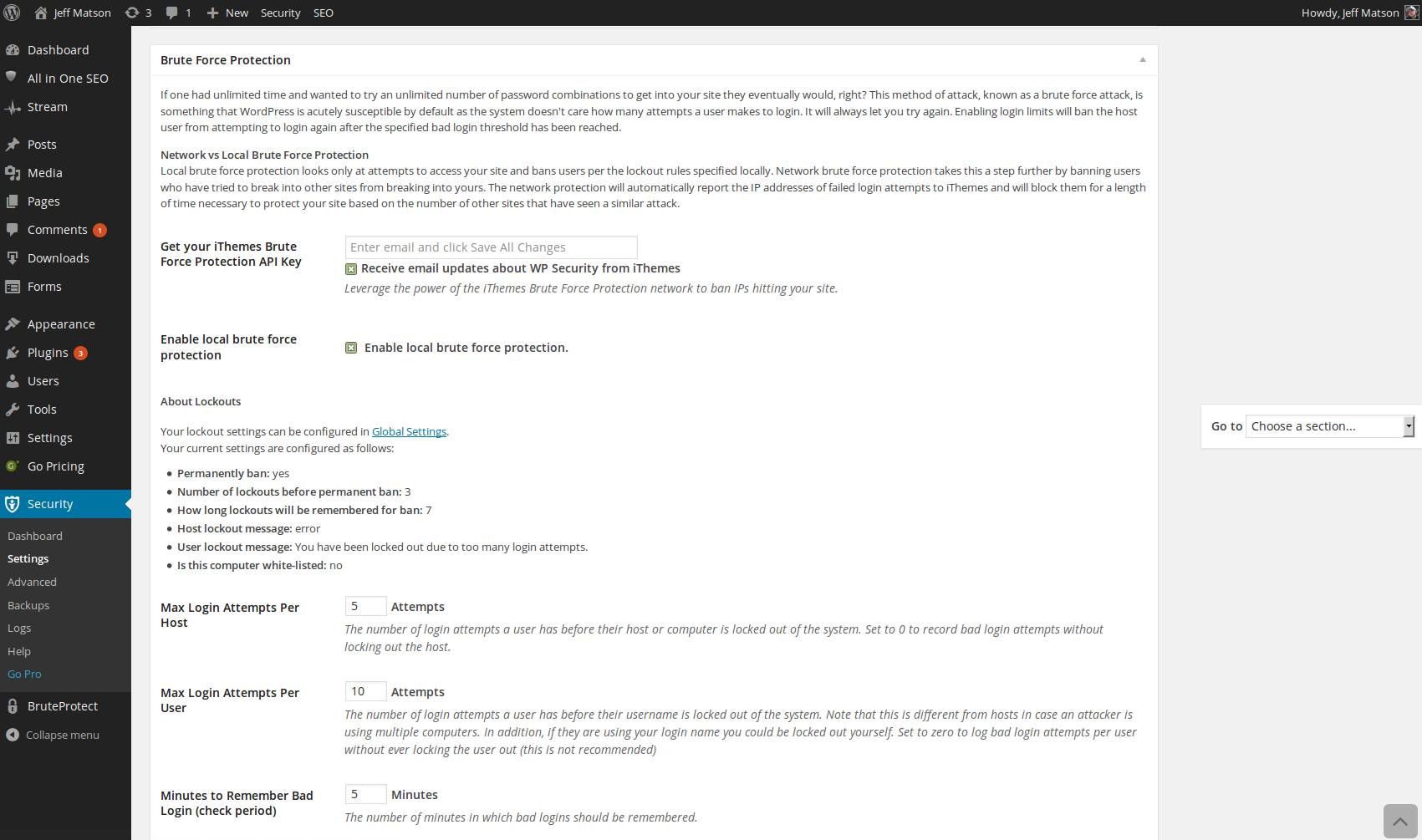
To use iThemes Security’s network brute force protection global lockout rules to make protection against attacks much more effective, enter your email address into the Get your iThemes Brute Force Protection API Key field and click on Save All Changes at the bottom of the Brute Force Protection section.
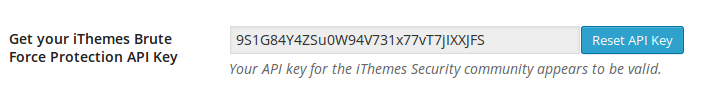
Once you enter your email address, your API key should be automatically entered for you within this field. Be sure that it states “Your API key for the iThemes Security community appears to be valid.” directly below this field.
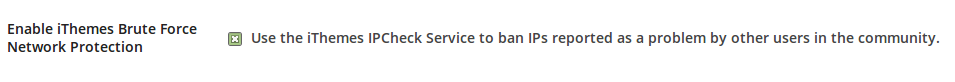
Next, you should see a checkbox labeled Enable iThemes Brute Force Network Protection. Check this box to allow connection from your site to iThemes for obtaining IPs that have been reported by the community as known brute force sources.
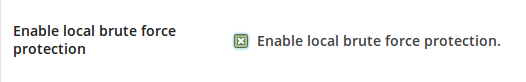
If you would like to enable brute force protection locally on your site in addition to the network brute force protection that iThemes provides, select the checkbox next to Enable local brute force protection.

Once the checkbox mentioned in the previous step is selected, you will be presented with various options to configure your local brute force protection. These options are Max Login Attempts Per Host, Max Login Attempts Per User, and Minutes to Remember Bad Login (check period). This means that with the default settings, an IP would be blocked if they fail to log in to any user 5 times, a user would be completely locked if that username fails to log in 10 times, and all failed logins would be kept on record for 5 minutes.
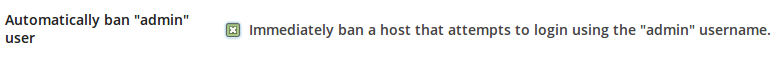
The final option, if local brute force protection is enabled, is Automatically ban “admin” user. As most brute force attacks will automatically target a user with the login name as admin, this is incredibly effective to enable. If you have a user with the username as admin, you will need to leave this unchecked to log in as that user, but we highly recommend renaming the admin user to something else.
- Once all your changes are made, click the Save All Changes button.
Become a master of WordPress plugins! Protect, optimize, secure, and expand the functionality of your website easily with the help of WordPress plugins!