See our related guide to enable DNSSEC on cPanel servers.
In this article, we cover how to implement domain name system security extensions (DNSSEC) with the Cloudflare content delivery network (CDN). This procedure is meant to work in sync with other DNS tools, whether you are altering your DNS records with a registrar or on you our managed VPS with cPanel.
DNSSEC provides an authentication layer by digitally signing a domain’s DNS records at the authoritative DNS server. With DNSSEC added to a domain, if the DNS cannot be authenticated because of an authorized DNS hop during network route, the requested website won’t display. This protects users against DNS spoofing and man-in-the-middle (MITM) attacks.
When you request DNSSEC with a DNS provider, such as Cloudflare, they sign your DNS zone and provide a resource records set (RRset) including the following:
- DNSKEY – public key which signs the RRset
- DS (delegation signer) record – hash of the DNSKEY
Below we’ll cover how to enable DNSSEC in Cloudflare and verify it.
To implement DNSSEC with Cloudflare, your registrar and top-level domain (TLD) must support it and Algorithm 13 (ECDSA Curve P-256 with SHA-256 hashing algorithm).
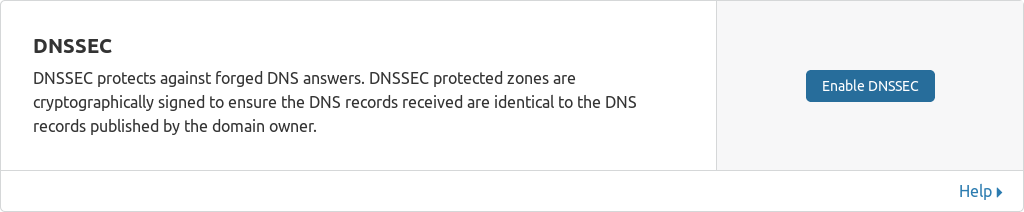
Enable DNSSEC

- Point your domain nameservers to Cloudflare.
- Log in to Cloudflare.com.
- Click DNS at the top.
- Click Enable DNSSEC.
- Send the DNSSEC records to your domain registrar to update DNS records.
Warning: Inputting DNSSEC records incorrectly may cause website downtime.
Verify DNSSEC
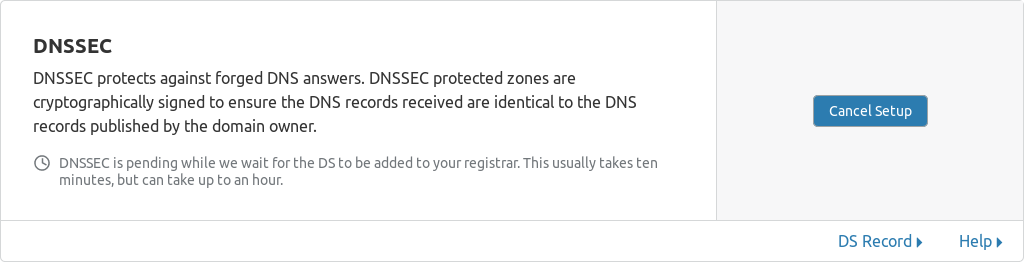
After your DNSSEC records are added, Cloudflare should verify it within 10 minutes, but it may take up to 2 hours. You can review your the records by clicking DS Record on the lower-right of the DNSSEC panel.
- Refresh your Cloudflare DNS page to check if the status states pending:
or Success!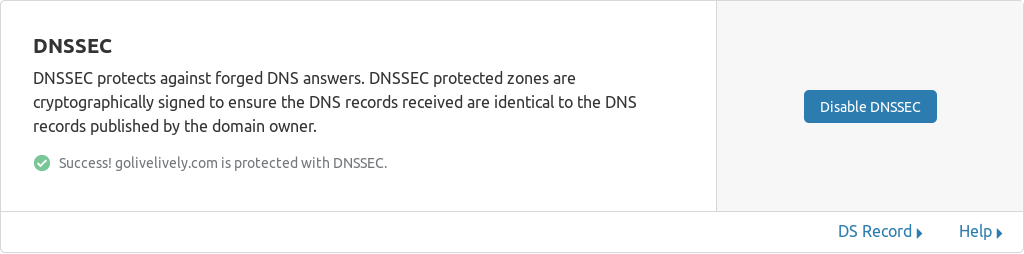
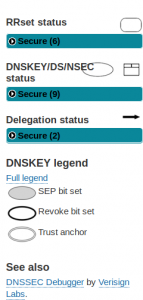
- Once it states Success! with a green checkmark, check your domain DNS key at DNSViz.net.
- You should only see Secure on the left.
Continue to improve website security with HTTP Strict Transport Security (HSTS) in Cloudflare or within your .htaccess file.
