WordPress content management system (CMS) tutorials focusing on security can help you find better ways to secure your website. Whether you’re a seasoned WordPress developer or a new user learning how to customize WordPress, there’s always something that could better secure your website.
Below we cover 10 ways to secure WordPress websites. Want the performance of a VPS without the extra features? Check out our Secure WordPress Hosting.
Secure WordPress at the Installation Level
Use Strong Passwords and Two-Factor Authentication
Follow recommended password practices. Create passwords over 15 characters with special characters, lower and upper case letters, and numbers. This should apply to user logins, connected databases, and salts set in the wp-config.php file.
Change passwords every 30-90 days and when someone leaves your team/organization. Consider password management tools such as KeyPass or Dashlane to manage and regularly update strong passwords.
Two-Factor Authentication is security that goes beyond just using a password. With two-factor authentication, you enter your password as normal, but then you are asked to take one more step to verify your identity. This second step usually comes in the form of a text or email verification code sent to your phone number or email address that you have on file with the account.
Even if a hacker steals your password, they won’t have access to your phone or email to intercept this message and break into your account. Learn how to enable two-factor authentication.
Security Plugins
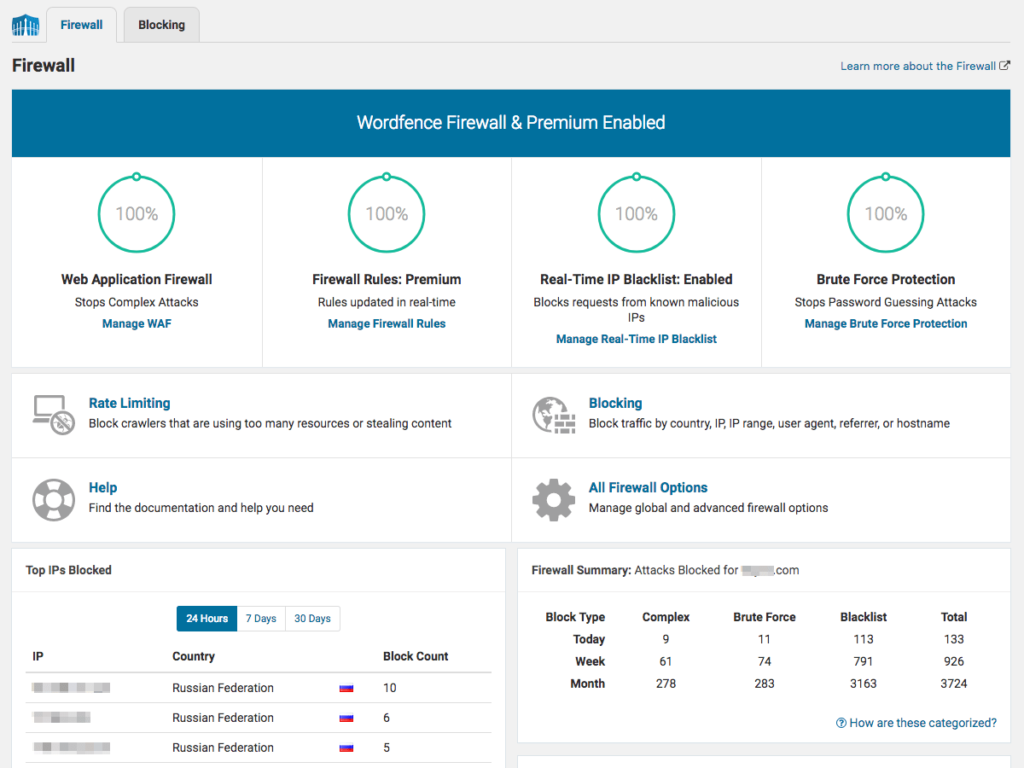
Install a security plugin and regularly monitor its logs. Important security plugin features include:
- Activity reports
- Alerts of plugins abandoned (haven’t been updated in months)
- Blocks abusive bots
- Brute force protection against login attempts
- Firewall with IP address whitelist/blacklist based on IP Range, Hostname, and User Agent
- Multifactor authentication with email or SMS verification
- Spam comment filtering
- File integrity scans for WordPress core files
We recommend Wordfence Security for securing WordPress sites from our list of security plugins.
Update Plugins/Themes
Keep your theme and plugins up to date. Furthermore, update cPanel when prompted in WebHost Manager (WHM) (VPS/Dedicated only) and use the latest stable version of PHP.
You can use the WordPress Site Health feature for instant recommendations on improving your security and performance.
Remove Outdated/Unneeded Addons
If you don’t need a plugin, or the plugin has one purpose – create tables or add social media icons – find a plugin (or theme) capable of multiple functions such as Jetpack and Storefront theme for WooCommerce.
Remember, every addon is a potential vulnerability. This is why it’s generally recommended to only have an active theme and a fallback theme.
Inactive users and FTP accounts should be removed as well.
Protect User Input Fields
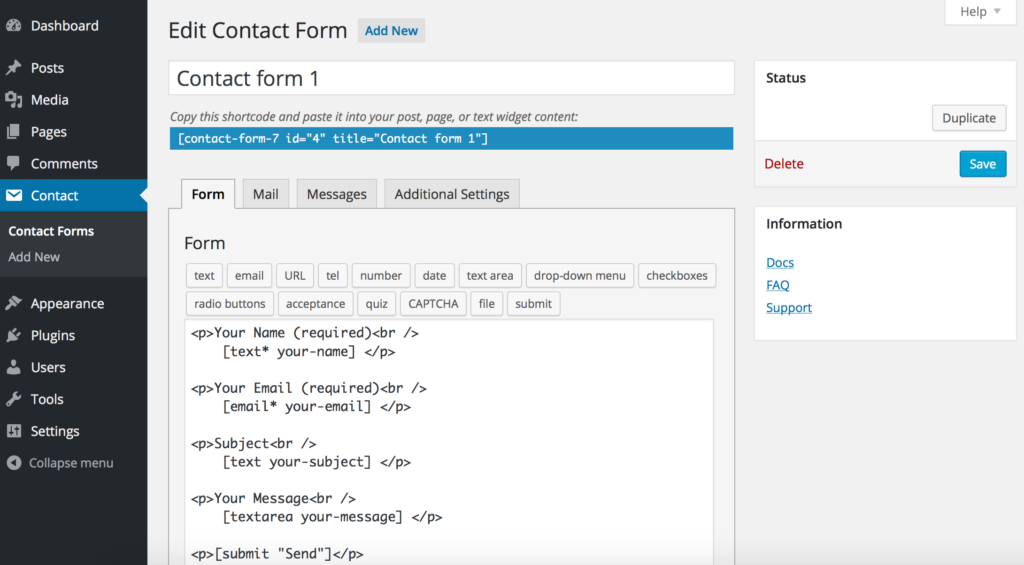
Contact forms, email subscription fields, and other text input fields should have input validation restrictions. For example, limit characters per field and disallow unnecessary special characters to prevent code injection.
For example, Contact Form 7 makes securing contact forms an easy task without needing to edit raw files.
Secure WordPress at the Server Level
Account Scans
Full account scans can catch malware in external directories – e.g. email accounts without strong authentication or subdomains using another CMS.
With an email ticket request, our Support department will scan your server space and send you the results. Although we’re not security professionals, we’ll do our best to provide resources to improve your security going forward.
VPS / Dedicated users can do this anytime with ClamAV.
Check out Monarx for enhanced hands-off website protection against malware, phishing, and other PHP-based exploits.

Backup Your Website Regularly
Create backups regularly using a backup plugin and cPanel. Security plugins don’t always catch issues before irreversible damage is done. Sometimes, the best course of action is complete hack recovery – restore from a backup and change all passwords.
Check out our Backup Manager in cPanel for automated backups.
Install an SSL Certificate
Use a free or paid SSL, then force redirects to HTTPS to assure visitors the website is secure. Websites with e-commerce functions should use a paid SSL while a free alternative such as AutoSSL, the free SSL that’s auto-enabled forever, suffices for others.
We recommend Really Simple SSL for fixing mixed content errors identified with online tools such as WhyNoPadlock.com.
Those looking for more security can configure HTTP Strict Transport Security (HSTS) to force SSL usage at the browser level.
Secure wp-config.php
Don’t neglect the wp-config.php file when changing passwords throughout your website. But other than the salt and database password, there are many other ways to customize the wp-config.php file for better security. Edit the file to add any code below at the bottom.
define( 'FORCE_SSL_ADMIN', true ); forces users to login with an HTTPS connection.
define( 'DISALLOW_FILE_EDIT', true ); ensures no one can edit raw plugin and theme files even with login credentials for your WordPress dashboard.
define( 'EMPTY_TRASH_DAYS', 30 ); sets trashed attachments, comments, posts, and pages to permanently delete after a set number of days (30 is the default)
Warning: With EMPTY_TRASH_DAYS set, users will NOT be asked for confirmation when clicking “Delete Permanently”.
Use Secure Connections
This is indirectly related to the WordPress website. When using Wi-Fi, ensure you’re using an authentic network instead of a rogue spoofed access point. Consider using a virtual private network (VPN) on Wi-Fi networks especially if they don’t require a password to connect – e.g. restaurants and hotels. This with an SSL helps fight man-in-the-middle attacks against potential hackers snooping for login credentials and other sensitive data.
Final Thoughts
Securing your WordPress website is a crucial step in the design process. With these 10 ways to secure WordPress, you can have the peace of mind that your site and data are safe.
Learn more about securing your website with our WordPress Education Channel.
Improve the performance and security of your WordPress website with our new WordPress VPS Hosting plans. Get 40x faster speeds with dedicated resources, server caching, and optimization tools.
High-Performance VPS
99.99% Uptime
Free SSL & Dedicated IP
Advanced Server Caching